The Buyer's Guide to Exposure Assessment Platforms
Table of Contents
The state of exposure management
Core capabilities of an EAP
The state of exposure management
Before diving into Exposure Assessment Platform (EAP) capabilities, let’s take a step back to first understand the state of exposure management and the pain points these solutions are designed to address.
The modern attack surface is vast and constantly evolving. Security teams are managing modern cloud infrastructure, work-from-home device policies, and legacy on-premise systems. New technologies introduce fresh risks while older infrastructure adds complexity.
The IT environment has evolved rapidly:
- First, it was on-premises servers and endpoints—straightforward and contained.
- The next wave brought mobility: laptops, smartphones, and remote devices that stretched the security perimeter.
- Now, we operate in a hyperconnected digital ecosystem where systems, devices, users, and software—constantly generate signals.
Missing any critical data point—whether from an unpatched system, an unmanaged device, an inactive user account, or outdated software—could mean an unnoticed exposure. Managing this environment without broad visibility and automation—and increasingly, AI—has become impossible due to its scale and complexity. This has driven the need for a continuous exposure management program and a platform to manage it.
Common challenges in exposure management
- Attack Surface Visibility – You can’t secure what you can’t see. Without a complete inventory of assets—devices, users, software, etc.—blind spots emerge and give adversaries easy entry points. Without the right tooling, there’s a significant cost of manual intervention to aggregate, correlate, and deduplicate data across siloed systems (sources of inventory). The sheer volume of signals and changes makes it impossible for manual processes to monitor and maintain this data.
- Vulnerability Prioritization – Which vulnerabilities are the most important, and why? This too requires significant manual intervention to correlate threat intelligence, assess exploitability and asset criticality, factor in security controls, and understand business impact—all in real time.
- Remediation Validation – Did you actually remove the risk? While IT service management (ITSM) platforms are essential to kicking off the remediation process, they lack the telemetry to go beyond a ticket closure. Without verification, teams are stuck in an endless loop of reopening workflows and struggling to close security gaps. Strong EAPs, with their continuous data ingestion, should give you insight into the presence and state of exposures, at all times, so validation is automatic.
The shift toward continuous exposure management
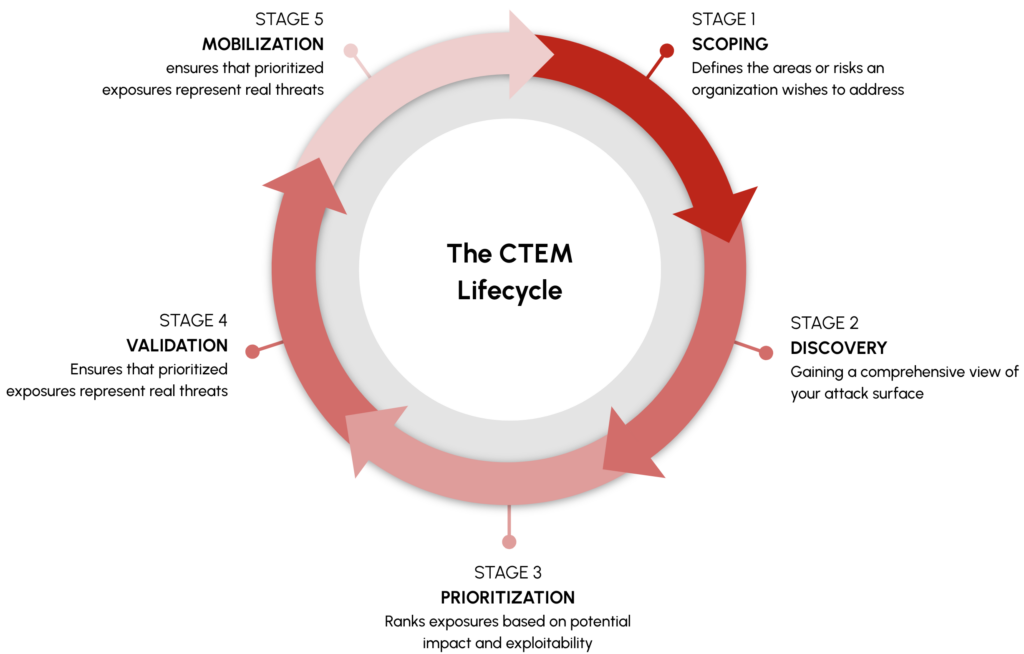
Exposure management can’t be treated as a series of disconnected tasks. Tackling today’s threats requires a unified, continuous approach. This is where continuous threat exposure management (CTEM) comes in, which is a structured process for teams to continuously identify, assess, prioritize, validate, and remediate exposures across the entire attack surface. CTEM provides a framework that makes an ever-growing attack surface manageable.
To power CTEM programs, EAPs have become the essential technology to drive the process forward. An EAP’s success depends on its ability to help your team continuously assess, prioritize, and mitigate risk across the entire attack surface.
EAPs provide the necessary visibility, automation, and risk-based insights to support each stage of the CTEM lifecycle:
- Scoping and Discovery: Provides visibility by continuously discovering assets, mapping the attack surface, and identifying exposures.
- Prioritization: Contextualizes risk based on severity, business impact, and likelihood of exploitation.
- Validation: Analyzes exposures to determine if they are exploitable in real-world conditions.
- Mobilization: Provides investigative guidance and automates remediation workflows to address critical risks.
By integrating with your existing systems and eliminating manual tasks, EAPs enable real-time prioritization and streamline remediation workflows. EAPs help you focus attention where it matters most—ranking exposures by severity, asset criticality, business impact, likelihood of exploitation, and security control context. The result? Smarter decisions driven by real risk, not noise. With an EAP, your security team can move from reactive firefighting to proactive defense where you can find and close gaps before adversaries can exploit them.
